US Labour Website Compromise Spreads Malware
Malware planted on the US Department of Labour’s website attacked victims’ systems using a zero-day bug in Internet Explorer 8
Hackers compromised the US Department of Labour’s website last week, modifying pages about nuclear-related illnesses with malware that could compromise visitors’ computers through a zero-day vulnerability in Internet Explorer 8, according to security experts.
While security firms first released details of the attack on 1 May, endpoint protection firm Invincea reported on 3 May that the malware served up by the Department of Labour’s pages used an exploit for a previously unknown flaw in Internet Explorer 8.
Poison Ivy malware
Victims’ systems which fell prey to the attack would be compromised with a variant of Poison Ivy, which is a malware type popular with Chinese hackers. In addition, the command-and-control traffic matches that seen in cases of espionage attributed to a Chinese attacker known as DeepPanda, according to security-management firm AlienVault.
 The attack follows reports of the theft of technology secrets, allegedly by Chinese agents, from Western military contractors.
The attack follows reports of the theft of technology secrets, allegedly by Chinese agents, from Western military contractors.
These recent attacks highlight the necessity for the US government to address the issue of nation-state espionage, Anup Ghosh, founder and chief executive at Invincea, told eWEEK.
“They are essentially stealing defence technology secrets right from under our noses; it’s pretty brazen,” he said. “At what point, do we as a nation, as a government, say enough is enough, that the red lines are being crossed here?”
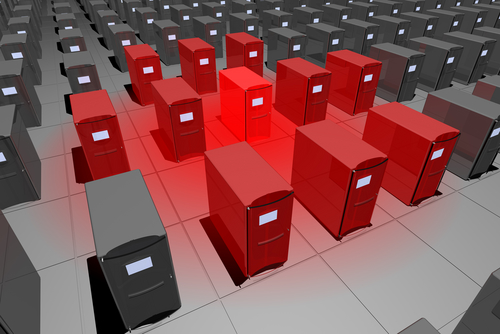
The compromise at the Department of Labour appears to be a version of a tactic known as a watering hole attack, where the attackers compromise a site that they believe will be visited by their intended targets.
Watering hole attacks
Unlike more general drive-by download attacks, which attempt to compromise as many PCs as possible, watering hole attacks are a form of targeted operation.
In September, security firm Symantec issued an in-depth report on a series of attacks, known as the Elderwood Project, in which attackers applied a number of zero-day exploits and used watering holes to target certain companies or types of companies.
In December, attackers compromised the Council of Foreign Relations’ website and used it to serve up malware using an exploit for a previously unknown flaw in Internet Explorer 6, 7 and 8. While experts cannot be certain that officials at the US Department of Energy were the targets of the attack, the logic is clear, said Ghosh.
Nuclear secrets
“The pages that were compromised with the malware were specific to this issue of workers and nuclear toxicity,” he said. “The DOE – and its many labs – do a lot of nuclear research.”
As in many cases of targeted attacks, the malware used by the attackers was not well recognised by antivirus software – only two out of 46 products identified the malicious executable, according to the initial post by Invincea.
Users who believe they may be at risk from this attack should use a different browser or any of a variety of security virtualisation products that isolate browsers from the rest of the system.
“Invincea has been notified that Microsoft is aware of this vulnerability and is currently investigating,” the company said in its post.
Are you a security pro? Try our quiz!
Originally published on eWeek.